Magento recently released a new security patch (SUPEE-7405) that is included in Enterprise Edition 1.14.2.3 and Community Edition 1.9.2.3 to address multiple vulnerabilities, including several critical cross scripting, information leakage / disclosure, and cross-site request forgery vulnerabilities. Magento recently released a new security patch (SUPEE-6788) that is included in Enterprise Edition 1.14.2.2 and Community Edition 1.9.2.2 to address multiple issues, including remote code execution and information leak vulnerabilities. The patch is unrelated to the recent Guruincsite malware issue. Today when i logged into my magento store admin, it shown a new critical message like Critical Reminder: Download and install Magento security patches. Download now.
SUPEE-8788, Enterprise Edition 1.14.3 and Community Edition 1.9.3 address Zend framework and payment vulnerabilities, ensure sessions are invalidated after a user logs out, and make several other security enhancements that are detailed below.
Information on additional functional enhancements available the new 1.14.3 and 1.9.3 releases is available in the Enterprise Edition and Community Edition release notes.
Patches and upgrades are available for the following Magento versions:
-
Enterprise Edition 1.9.0.0-1.14.2.4: SUPEE-8788 or upgrade to Enterprise Edition 1.14.3
-
Community Edition 1.5.0.1-1.9.2.4: SUPEE-8788 or upgrade to Community Edition 1.9.3
To download a patch or release, choose from the following options:
Partners:
|
Enterprise Edition 1.14.3 |
Partner Portal > Magento Enterprise Edition > Magento Enterprise Edition 1.X > Magento Enterprise Edition 1.x > Version 1.x Releases > Version 1.14.3 |
|
SUPEE-8788 |
Partner Portal > Magento Enterprise Edition > Magento Enterprise Edition 1.X > Magento Enterprise Edition 1.x > Support and Security Patches > Security Patches > Security Patches – October 2016 |
Enterprise Edition Merchants:
|
Enterprise Edition 1.14.3 |
My Account > Downloads Tab > Magento Enterprise Edition 1.X > Magento Enterprise Edition 1.x > Version |
|
SUPEE-8788 |
My Account > Downloads Tab > Magento Enterprise Edition 1.X > Magento Enterprise Edition 1.x > Support and Security Patches > Security Patches > Security Patches – October 2016 |
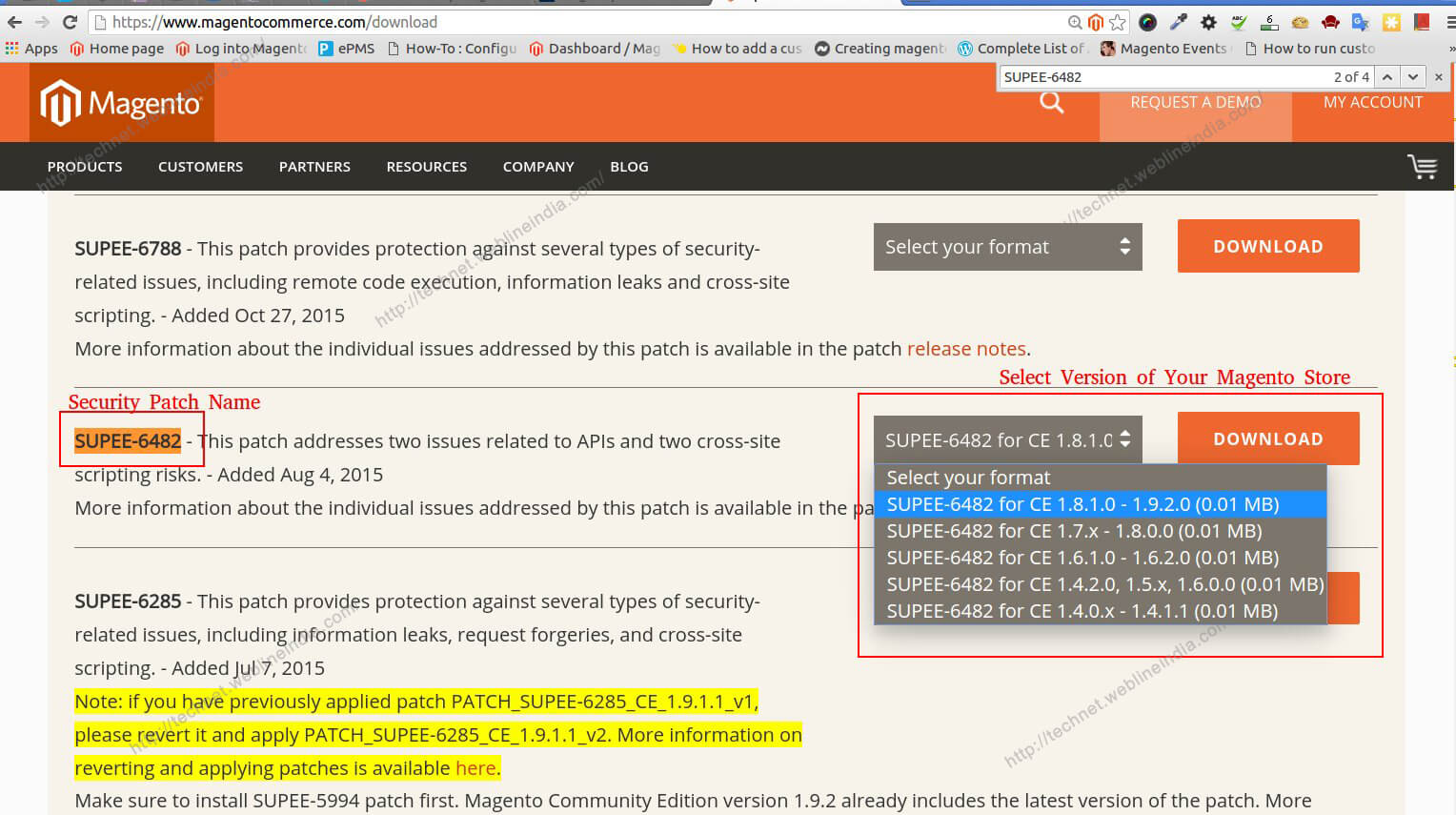
Download Security Patch From Microsoft Website
Community Edition Merchants:
|
Community Edition 1.9.3 |
Community Edition Download Page > Release Archive Tab |
|
SUPEE-8788 |
Community Edition Download Page > Release Archive Tab > Magento Community Edition Patches - 1.x Section |
| APPSEC-1484 - Remote Code Execution in checkout | |
|---|---|
| Type: | Remote Code Execution (RCE) |
| CVSSv3 Severity: | 9.8 (Critical) |
| Known Attacks: | None |
| Description: |
With some payment methods it might be possible to execute malicious PHP code during checkout. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1480 - SQL injection in Zend Framework | |
|---|---|
| Type: | SQL Injection/Improper validation |
| CVSSv3 Severity: | 9.1 (Critical) |
| Known Attacks: | None |
| Description: |
A bug in Zend Framework value escaping allows a malicious user to inject SQL through the ordering or grouping parameters. While there are no known frontend entry point vulnerabilities that would allow for a full SQL injection, we’ve found an entry point in the Magento Admin panel, and other entry points most likely exist. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1488 - Stored XSS in invitations | |
|---|---|
| Type: | Cross-Site Scripting (XSS) - Stored |
| CVSSv3 Severity: | 8.2 (High) |
| Known Attacks: | None |
| Description: |
It is possible to use the Magento Enterprise Edition invitations feature to insert malicious JavaScript that might be executed in the admin context. |
| Product(s) Affected: | Magento EE prior to 1.14.3 |
| Fixed In: | EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1247 - Block cache exploit | |
|---|---|
| Type: | Information Leakage |
| CVSSv3 Severity: | 7.7 (High) |
| Known Attacks: | None |
| Description: |
With access to any CMS functionality, an attacker with administrator permissions can use blocks to exfiltrate information stored in cache. This sensitive information includes store configuration, encryption key, and database connection details. Additionally, it might be possible to execute code. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1517 - Log in as another customer | |
|---|---|
| Type: | Insufficient data protection |
| CVSSv3 Severity: | 7.5 (High) |
| Known Attacks: | None |
| Description: |
In certain configurations, it is possible to log in as existing store customer while knowing only his email address, not his password. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1375 - Remote Code Execution in admin | |
|---|---|
| Type: | Remote code execution (RCE) |
| CVSSv3 Severity: | 6.5 (Medium) |
| Known Attacks: | None |
| Description: |
The import/export functionality in Magento unserializes data supplied from the Admin dashboard without proper checks. This can lead to possible code execution if a malicious user has Magento Admin access, even if access is limited to the import/export functionality. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |

| APPSEC-1338 - Full Page Cache poisoning | |
|---|---|
| Type: | Cache Poisoning |
| CVSSv3 Severity: | 6.5 (Medium) |
| Known Attacks: | None |
| Description: |
It is possible to manipulate the full page cache to store incorrect pages under regular page URL entries. This issue affects only Magento Enterprise Edition. |
| Product(s) Affected: | Magento EE prior to 1.14.3 |
| Fixed In: | EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1436 - XSS vulnerability in URL processing | |
|---|---|
| Type: | Cross-site Scripting (XSS) |
| CVSSv3 Severity: | 6.1 (Medium) |
| Known Attacks: | None |
| Description: |
Magento function related to URL processing incorrectly uses user-supplied data from request headers. This can result in a cross-site scripting issue. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Internal/support |
| APPSEC-1211 - XSS in categories management | |
|---|---|
| Type: | Cross-site Scripting (XSS) |
| CVSSv3 Severity: | 6.1 (Medium) |
| Known Attacks: | None |
| Description: |
It is possible to create a category that contains malicious JavaScript code in the category name. This code will then be executed in other parts of the Admin panel, such as URL Rewrites. To exploit this issue, a user would need admin access to catalog management. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Milan A. Solanki |
| APPSEC-1058 - GIF flooding | |
|---|---|
| Type: | Denial of Service (DoS) |
| CVSSv3 Severity: | 5.3 (Medium) |
| Known Attacks: | None |
| Description: |
A malicious user can upload a modified image that could cause a script timeout, resulting in a denial of service attack. (This potential vulnerability affects stores that allow users to upload images as a custom option or through the Admin dashboard) |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Shahmeer Baloch |
| APPSEC-666 - Cross-site scripting in Flash file uploader | |
|---|---|
| Type: | Cross-Site Scripting (XSS) - reflected |
| CVSSv3 Severity: | 5.3 (Medium) |
| Known Attacks: | None |
| Description: |
Reflected cross-site scripting is possible on sites that use the file custom option. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Francisco Javier Correa Silva |
| APPSEC-1282: Filter avoidance | |
|---|---|
| Type: | Filter avoidance |
| CVSSv3 Severity: | 4.9 (Medium) |
| Known Attacks: | None |
| Description: |
Implementing filters for XSS in email templates and other Admin features might not be sufficient to stop specially crafted exploit strings. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-327 - CSRF in several forms | |
|---|---|
| Type: | Cross-site Request Forgery (CSRF) |
| CVSSv3 Severity: | 4.7 (Medium) |
| Known Attacks: | None |
| Description: |
Improper form key validation leads to possible CSRF attacks on several forms throughout Magento. As a result, a malicious user could create a phishing form that, when clicked by a user, would execute an action such as update cart or login. Note: This issue affects only older versions of Magento. |
| Product(s) Affected: | Magento CE prior to 1.8.1, and Magento EE prior to 1.13.1 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Internal |
| APPSEC-1189 - CSRF on removing item from Wishlist or Address Book | |
|---|---|
| Type: | Cross-site Request Forgery (CSRF) |
| CVSSv3 Severity: | 4.7 (Medium) |
| Known Attacks: | None |
| Description: |
It is possible to create a phishing page that if visited by a store customer would delete the customer’s address or wishlist items. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3 |
| Reporter: | High-Tech Bridge Security Research |
| APPSEC-1478: Session does not expire on logout | |
|---|---|
| Type: | Insufficient Session Expiration |
| CVSSv3 Severity: | 4.2 (Medium) |
| Known Attacks: | None |
| Description: |
Session do not expire after logout, making it possible to steal session cookies and access a customer’s account. This risk primarily occurs when users share a computer to access the site. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Mahmoud Osama |
| APPSEC-1106 - Lack of certificate validation enables MitM attacks | |
|---|---|
| Type: | Man-in-the-Middle (MitM) |
| CVSSv3 Severity: | 3.7 (Low) |
| Known Attacks: | None |
| Description: |
Lack of certificate validation on calls to external services enables man-in-the-middle attacks on those calls. This results in possible disclosure of customer information. The risk is low due to the effort needed to execute such an attack. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Maksymilian Arciemowicz |
| APPSEC-995 - Timing attack on hash checking | |
|---|---|
| Type: | Timing attack |
| CVSSv3 Severity: | 3.7 (Low) |
| Known Attacks: | None |
| Description: |
It is theoretically possible to execute a timing attack on the password checking functionality. This is a low-risk vulnerability due to the effort required to execute this attack successfully. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Teguh P. Alko |
Windows Security Patch
Please refer to Security Best Practices for additional information how to secure your site.
Be sure to implement and test the patch in a development environment first to confirm that it works as expected before deploying it to a production site.
SUPEE-8788, Enterprise Edition 1.14.3 and Community Edition 1.9.3 address Zend framework and payment vulnerabilities, ensure sessions are invalidated after a user logs out, and make several other security enhancements that are detailed below.
Information on additional functional enhancements available the new 1.14.3 and 1.9.3 releases is available in the Enterprise Edition and Community Edition release notes.
Patches and upgrades are available for the following Magento versions:
-
Enterprise Edition 1.9.0.0-1.14.2.4: SUPEE-8788 or upgrade to Enterprise Edition 1.14.3
-
Community Edition 1.5.0.1-1.9.2.4: SUPEE-8788 or upgrade to Community Edition 1.9.3
To download a patch or release, choose from the following options:
Partners:
|
Enterprise Edition 1.14.3 |
Partner Portal > Magento Enterprise Edition > Magento Enterprise Edition 1.X > Magento Enterprise Edition 1.x > Version 1.x Releases > Version 1.14.3 |
|
SUPEE-8788 |
Partner Portal > Magento Enterprise Edition > Magento Enterprise Edition 1.X > Magento Enterprise Edition 1.x > Support and Security Patches > Security Patches > Security Patches – October 2016 |
Enterprise Edition Merchants:
|
Enterprise Edition 1.14.3 |
My Account > Downloads Tab > Magento Enterprise Edition 1.X > Magento Enterprise Edition 1.x > Version |
|
SUPEE-8788 |
My Account > Downloads Tab > Magento Enterprise Edition 1.X > Magento Enterprise Edition 1.x > Support and Security Patches > Security Patches > Security Patches – October 2016 |
Community Edition Merchants:
|
Community Edition 1.9.3 |
Community Edition Download Page > Release Archive Tab |
|
SUPEE-8788 |
Community Edition Download Page > Release Archive Tab > Magento Community Edition Patches - 1.x Section |
| APPSEC-1484 - Remote Code Execution in checkout | |
|---|---|
| Type: | Remote Code Execution (RCE) |
| CVSSv3 Severity: | 9.8 (Critical) |
| Known Attacks: | None |
| Description: |
With some payment methods it might be possible to execute malicious PHP code during checkout. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1480 - SQL injection in Zend Framework | |
|---|---|
| Type: | SQL Injection/Improper validation |
| CVSSv3 Severity: | 9.1 (Critical) |
| Known Attacks: | None |
| Description: |
A bug in Zend Framework value escaping allows a malicious user to inject SQL through the ordering or grouping parameters. While there are no known frontend entry point vulnerabilities that would allow for a full SQL injection, we’ve found an entry point in the Magento Admin panel, and other entry points most likely exist. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1488 - Stored XSS in invitations | |
|---|---|
| Type: | Cross-Site Scripting (XSS) - Stored |
| CVSSv3 Severity: | 8.2 (High) |
| Known Attacks: | None |
| Description: |
It is possible to use the Magento Enterprise Edition invitations feature to insert malicious JavaScript that might be executed in the admin context. |
| Product(s) Affected: | Magento EE prior to 1.14.3 |
| Fixed In: | EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1247 - Block cache exploit | |
|---|---|
| Type: | Information Leakage |
| CVSSv3 Severity: | 7.7 (High) |
| Known Attacks: | None |
| Description: |
With access to any CMS functionality, an attacker with administrator permissions can use blocks to exfiltrate information stored in cache. This sensitive information includes store configuration, encryption key, and database connection details. Additionally, it might be possible to execute code. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1517 - Log in as another customer | |
|---|---|
| Type: | Insufficient data protection |
| CVSSv3 Severity: | 7.5 (High) |
| Known Attacks: | None |
| Description: |
In certain configurations, it is possible to log in as existing store customer while knowing only his email address, not his password. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1375 - Remote Code Execution in admin | |
|---|---|
| Type: | Remote code execution (RCE) |
| CVSSv3 Severity: | 6.5 (Medium) |
| Known Attacks: | None |
| Description: |
The import/export functionality in Magento unserializes data supplied from the Admin dashboard without proper checks. This can lead to possible code execution if a malicious user has Magento Admin access, even if access is limited to the import/export functionality. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1338 - Full Page Cache poisoning | |
|---|---|
| Type: | Cache Poisoning |
| CVSSv3 Severity: | 6.5 (Medium) |
| Known Attacks: | None |
| Description: |
It is possible to manipulate the full page cache to store incorrect pages under regular page URL entries. This issue affects only Magento Enterprise Edition. |
| Product(s) Affected: | Magento EE prior to 1.14.3 |
| Fixed In: | EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-1436 - XSS vulnerability in URL processing | |
|---|---|
| Type: | Cross-site Scripting (XSS) |
| CVSSv3 Severity: | 6.1 (Medium) |
| Known Attacks: | None |
| Description: |
Magento function related to URL processing incorrectly uses user-supplied data from request headers. This can result in a cross-site scripting issue. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Internal/support |
| APPSEC-1211 - XSS in categories management | |
|---|---|
| Type: | Cross-site Scripting (XSS) |
| CVSSv3 Severity: | 6.1 (Medium) |
| Known Attacks: | None |
| Description: |
It is possible to create a category that contains malicious JavaScript code in the category name. This code will then be executed in other parts of the Admin panel, such as URL Rewrites. To exploit this issue, a user would need admin access to catalog management. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Milan A. Solanki |
| APPSEC-1058 - GIF flooding | |
|---|---|
| Type: | Denial of Service (DoS) |
| CVSSv3 Severity: | 5.3 (Medium) |
| Known Attacks: | None |
| Description: |
A malicious user can upload a modified image that could cause a script timeout, resulting in a denial of service attack. (This potential vulnerability affects stores that allow users to upload images as a custom option or through the Admin dashboard) |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Shahmeer Baloch |
| APPSEC-666 - Cross-site scripting in Flash file uploader | |
|---|---|
| Type: | Cross-Site Scripting (XSS) - reflected |
| CVSSv3 Severity: | 5.3 (Medium) |
| Known Attacks: | None |
| Description: |
Reflected cross-site scripting is possible on sites that use the file custom option. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Francisco Javier Correa Silva |
| APPSEC-1282: Filter avoidance | |
|---|---|
| Type: | Filter avoidance |
| CVSSv3 Severity: | 4.9 (Medium) |
| Known Attacks: | None |
| Description: |
Implementing filters for XSS in email templates and other Admin features might not be sufficient to stop specially crafted exploit strings. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Peter O'Callaghan |
| APPSEC-327 - CSRF in several forms | |
|---|---|
| Type: | Cross-site Request Forgery (CSRF) |
| CVSSv3 Severity: | 4.7 (Medium) |
| Known Attacks: | None |
| Description: |
Improper form key validation leads to possible CSRF attacks on several forms throughout Magento. As a result, a malicious user could create a phishing form that, when clicked by a user, would execute an action such as update cart or login. Note: This issue affects only older versions of Magento. |
| Product(s) Affected: | Magento CE prior to 1.8.1, and Magento EE prior to 1.13.1 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Internal |
| APPSEC-1189 - CSRF on removing item from Wishlist or Address Book | |
|---|---|
| Type: | Cross-site Request Forgery (CSRF) |
| CVSSv3 Severity: | 4.7 (Medium) |
| Known Attacks: | None |
| Description: |
It is possible to create a phishing page that if visited by a store customer would delete the customer’s address or wishlist items. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3 |
| Reporter: | High-Tech Bridge Security Research |
| APPSEC-1478: Session does not expire on logout | |
|---|---|
| Type: | Insufficient Session Expiration |
| CVSSv3 Severity: | 4.2 (Medium) |
| Known Attacks: | None |
| Description: |
Session do not expire after logout, making it possible to steal session cookies and access a customer’s account. This risk primarily occurs when users share a computer to access the site. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Mahmoud Osama |
| APPSEC-1106 - Lack of certificate validation enables MitM attacks | |
|---|---|
| Type: | Man-in-the-Middle (MitM) |
| CVSSv3 Severity: | 3.7 (Low) |
| Known Attacks: | None |
| Description: |
Lack of certificate validation on calls to external services enables man-in-the-middle attacks on those calls. This results in possible disclosure of customer information. The risk is low due to the effort needed to execute such an attack. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Maksymilian Arciemowicz |
| APPSEC-995 - Timing attack on hash checking | |
|---|---|
| Type: | Timing attack |
| CVSSv3 Severity: | 3.7 (Low) |
| Known Attacks: | None |
| Description: |
It is theoretically possible to execute a timing attack on the password checking functionality. This is a low-risk vulnerability due to the effort required to execute this attack successfully. |
| Product(s) Affected: | Magento CE prior to 1.9.3, and Magento EE prior to 1.14.3 |
| Fixed In: | CE 1.9.3, EE 1.14.3, SUPEE-8788 |
| Reporter: | Teguh P. Alko |
Please refer to Security Best Practices for additional information how to secure your site.
Be sure to implement and test the patch in a development environment first to confirm that it works as expected before deploying it to a production site.